If you’ve done your best to stay away offline for the past two days so you could actually enjoy your weekend, you undoubtedly now find yourself trying to catch up on all the news surrounding WannaCry ransomware. This unprecedented malware attack began sweeping the globe late last week, and security researchers estimated that nearly 57,000 computers in more than 150 countries were infected by the end of the day on Friday.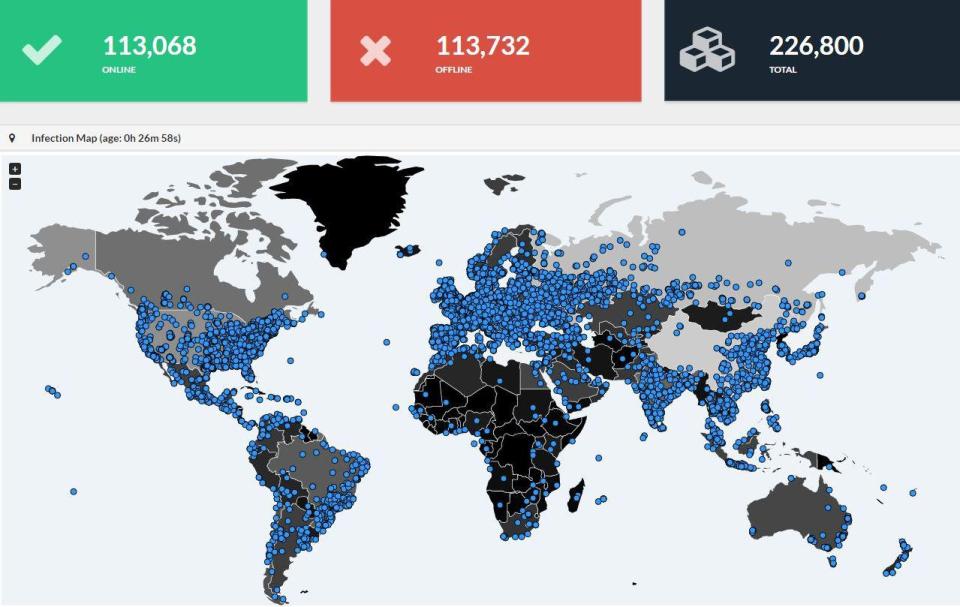
Remove in WINDOWS :
What does ransomware do?
There are different types of ransomware. However, all of them will prevent you from using your PC normally, and they will all ask you to do something before you can use your PC.
They can target any PC users, whether it’s a home computer, endpoints in an enterprise network, or servers used by a government agency or healthcare provider.
Ransomware can:
- Prevent you from accessing Windows.
- Encrypt files so you can’t use them.
- Stop certain apps from running (like your web browser).
Ransomware will demand that you pay money (a “ransom”) to get access to your PC or files. We have also seen them make you complete surveys.
There is no guarantee that paying the fine or doing what the ransomware tells you will give access to your PC or files again.
FAKE WARNING MESSAGE
Removal procedures :
- You can regain control of your web browser without paying anything by closing the warning message using the Task Manager.
- When you reopen your browser, make sure you don’t click Restore previous session.
- Read more about this threat in the Ransom:JS/FakeBsod.A description.
Remove in MAC:
NO WORRIES !!! Wanna Cry targets the patch work in WINDOWS only… So,
MAC USERS
DON’T WORRY
BE HAPPY !!!
Put simply, no. WannaCry takes advantage of a bug in Microsoft Windows’ network file sharing system, a technology called SMB. Once WannaCry gets onto a single computer on the network – usually because an individual opened a rogue email attachment – it then uses a bug in SMB to inject itself into all other computers on the network that haven’t been patched.
Macs also use SMB as the default network file sharing technology, so you might initially think Macs could be affected too. However, Apple uses its own bespoke implementation of SMB. While this is fully compatible with Microsoft’s version, it doesn’t suffer from the same bugs or security holes, so isn’t affected by WannaCry – or at least not in WannaCry’s current manifestation.
The iPhone, iPad, Apple TV and even the Apple Watch don’t use SMB file sharing, so aren’t even theoretically at risk from WannaCry.

Leave a comment